Cyber security ABC – how to get started
This page contains information on how an aviation organisation can get started with developing its cyber security management and what the key elements of that work are.

Initially, it can be challenging to see what aviation cyber security means from the perspective of your own organisation’s functions. Organisations’ functions and their potential impact on aviation security vary greatly. The essential thing is that each organisation assesses and identifies the significance of aviation cyber security in their operations. The end result of the assessment may vary by organisation. The result can be that cyber security has no impact or only minor impact on an organisations' systems, functions or risks critical to aviation. At the same time, an organisation may also discover that cyber security plays a key role in its functions and systems, and identify a need to develop its cyber security management.
Guidance and instructions from well-known and commonly used frameworks
A number of good practices, frameworks and standards apply to cyber security management. These include e.g. the ISO 27000 series, the NIST Cyber Security Framework, the Cybersecurity Capability Maturity Model (C2M2), other industrial standards and the Cybermeter published and maintained by the National Cyber Security Centre Finland. Sector-specific aviation standards are developed e.g. by EUROCAE. A framework can help you chart and assess the operations of your own organisation, allowing you to see the big picture.
As the Legislation on aviation cyber security page describes, the regulation on aviation cyber security is currently under extensive development and renewal. The application of the Part-IS regulation will harmonise the requirements, while bringing aviation organisations more widely under the scope of the requirements. The instructions below refer to currently applicable requirements and provide related tips from different frameworks. Traficom does not require you to use any particular framework. However, the instructions describe the key elements whose existence and implementation Traficom oversees as part of the cyber security management of organisations.
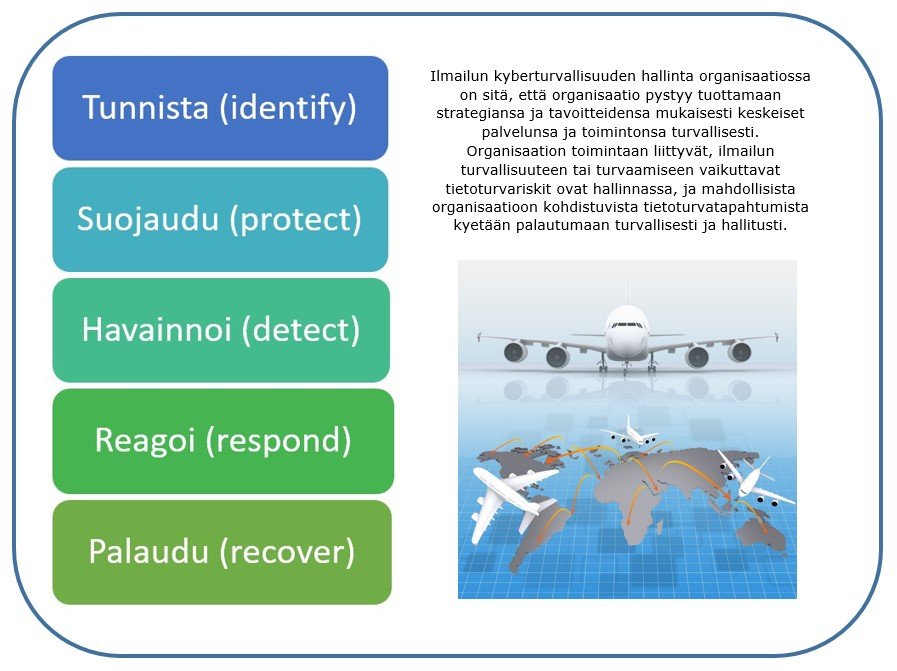
The drop-down menus under the image provide further information on the areas of cyber security management (identify, protect, detect, respond, recover). Each organisation takes care of their overall information security management based on their own needs and legislation coming from different sectors in society. The information security management measures described in the text refer to information security management from the aviation perspective (aviation safety, aviation security and resilience).